Don’t Fall for These Classic Email Phishing Tactics

Despite the cute fishing analogies, phishing emails are anything but. As hackers get more targeted and sophisticated with their phishing attempts, it’s important to be informed on what they’re currently doing so you know what to look for.
Below are some classic phishing examples that are being used in 2021 to target businesses and individuals.
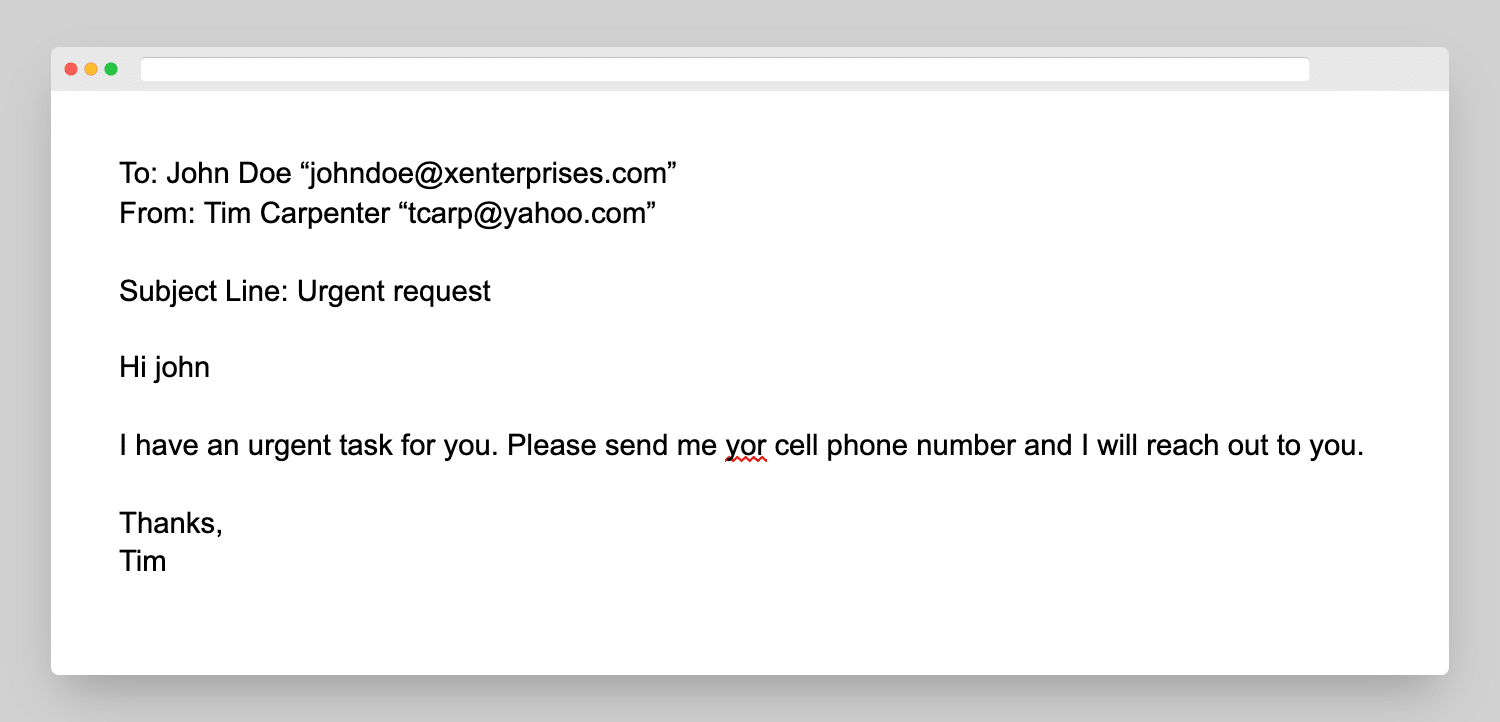
Email from your CEO
Chances are, your CEO will never ask you for money or your personal information via email. If you receive an email from someone claiming to be your company’s leader, take a minute to examine the rest of the email to validate it.
Be on high alert if your email provider flags certain emails with the below:
CAUTION: This email originated from outside your organization. Exercise caution when opening attachments or clicking links, especially from unknown senders.
Email from your HR/IT Department
HR and IT departments across the nation had to pivot on a dime to accommodate remote work and navigate complicated federal bills last year, which required extra correspondence with internal teams. Thus, a new phishing tactic was born. Acting as your HR or IT department, hackers will request information from employees or pretend to distribute policy changes, including malicious links.
These are the top 5 email subject lines from HR-related phishing emails:
- Password Check Required Immediately
- Vacation Policy Update
- Important: Dress Code Changes
- ACH Payment Receipt
- Test of the [COMPANY] Emergency Notification System
Most internal HR and IT teams will notify teams about policy changes or other updates in multiple ways and will rarely only send email correspondence. If there is ever a question about whether or not an email is legitimate, reach out to your IT contact.
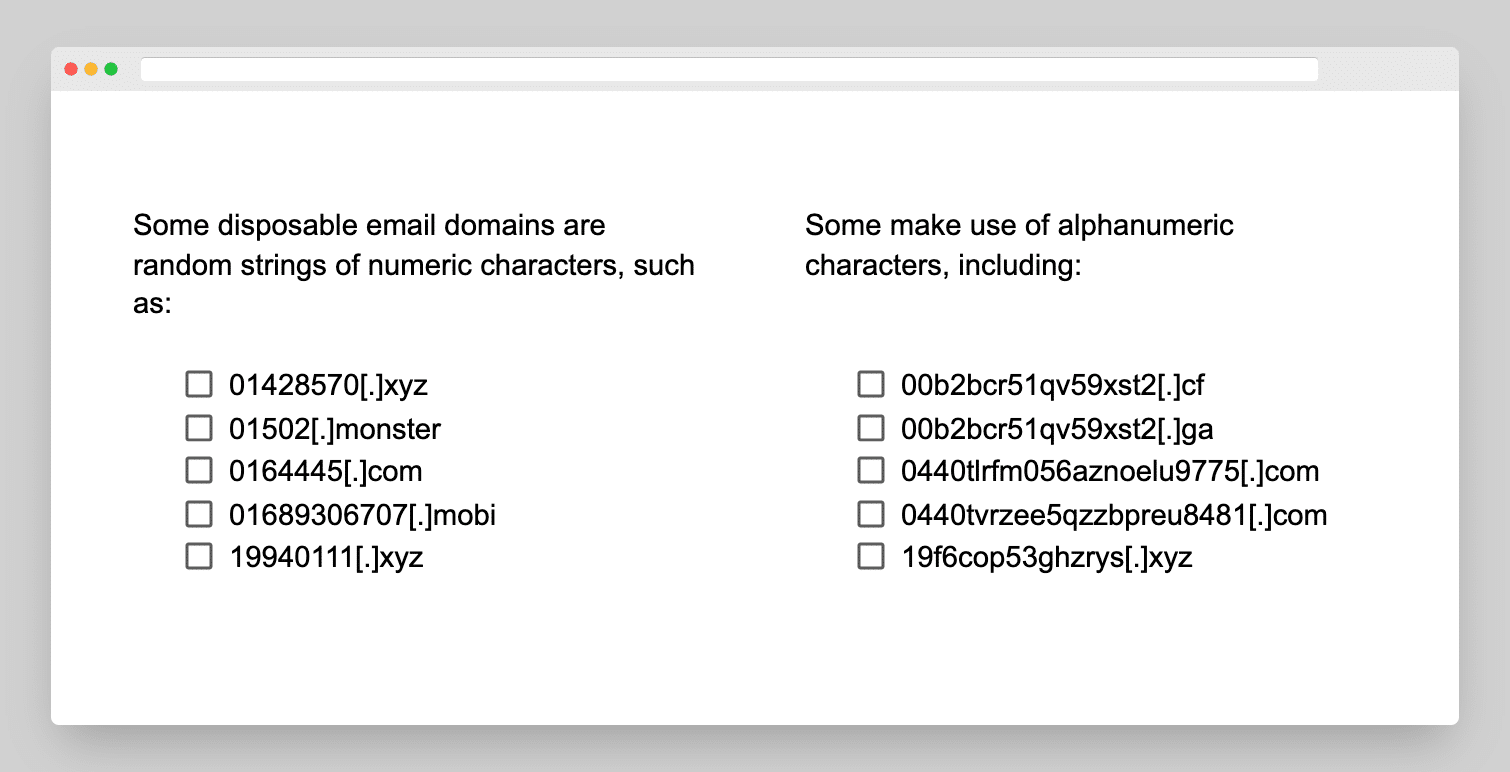
Suspicious Email Domains
Hackers often buy email domains to use to send their phishing emails. More often than not, the email domain alone can be a telltale sign that something is off. For example, if you received an email from your CEO, but the domain was a Yahoo! account or from an unrelated business, it’s a phishing email.
Requests to Update Your Information
Emails that unexpectedly request you verify account information by clicking a link, or include requests for certain financial documents, should get another critical look. These emails could look like legitimate outreach from social media accounts, banking institutions, or even your own HR department. But most reputable companies and organizations will not request this type of information via email.
COVID-19 Information
Unfortunately, hackers are using the COVID-19 pandemic to target people looking for vaccinations or information. There are several legitimate resources and organizations that send out emails to enable individuals to sign up for vaccines. However, if you receive an email from an unfamiliar company, or even if you receive correspondence from what you think is a reputable company, be critical of the email and the sender before you click any links or open any attachments.
What to Do With a Phishing Email
OK, so you opened an email that you suspect is a phishing attempt. Don’t panic, there are clear steps to take to ensure your information won’t be compromised.
- Do not click any links or buttons within the email.
- Do not open any attached images or documents.
- Report the email as needed to:
- Your company
- Your email provider
- A government body
- The organization the email is allegedly from
- Delete the email.
- Carry on with your day.
Millions and millions of phishing emails are sent every single day. While receiving a phishing email can be unsettling, if you’ve followed the steps above, you have nothing to worry about.
How to Protect Against Phishing Emails
The best thing you can do to protect yourself and your company from phishing emails is to stay educated and be critical of emails you weren’t expecting.
To prevent the threat of phishing emails before they can land in your inbox, your company’s IT infrastructure should include rigorous spam filters and email security solutions, as well as stringent password protection processes. That being said, it can be difficult to be certain your networks are up-to-date with the latest and greatest security measures for the ever-changing phishing landscape.
At SSE, we provide comprehensive IT solutions, including cybersecurity packages to make sure your networks are protecting your company and employee information.
Invest in some expert protection for your business. We can put our cybersecurity expertise to work for your business, implementing best practices, identifying vulnerabilities and protecting you against emerging cybersecurity threats.
Schedule a complimentary network scan with our team today!
Additional Blog Posts

CMMC Compliance Requirements Explained for Subcontractors
The Cybersecurity Maturity Model Certification (CMMC) has fundamentally changed what it means to participate in…
NIST 800-171 Rev.3 Draft: What It Means Now and Moving Forward With CMMC
The National Institute of Standards and Technology (NIST) finalized Special Publication (SP) 800-171 Revision 3…