What CMMC Level Do I Need to Attain?
Most Department of Defense (DoD) contractors understand that CMMC compliance is no longer optional. Where things may become unclear is determining which CMMC level actually applies to their organization.
With CMMC 2.0, the framework was simplified, but in practice, confusion still shows up. We see companies aim too low and get surprised during a solicitation review, or aim too high and invest time and money into controls they don’t actually need.
In real-world environments, the correct CMMC level typically comes down to a few practical factors: the type of data being handled, how systems are segmented, and what current or future contracts require. Once those pieces are understood, the path forward is usually straightforward.
This article walks through the current CMMC levels, what they are designed to protect, and how organizations typically determine which level applies to them.
What is the Difference Between CMMC Compliance Levels?
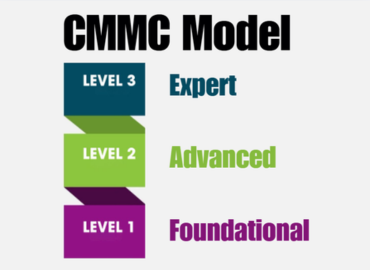
Under CMMC 2.0, the model consists of three levels. Each level aligns to the sensitivity of the information being handled and the level of oversight the DoD requires.
Higher levels don’t necessarily mean “better.” They simply reflect greater responsibility for protecting more sensitive data. The expectation increases as the potential impact of a data compromise increases.
| Level | Data Type / Purpose | Number of Practices / Controls | Assessment Type | Scope / Focus |
|---|---|---|---|---|
| Level 1 (Self-Assessment) | For managing Federal Contract Information (FCI) | 15 basic cybersecurity practices with 59 objectives (aligned with FAR 52.204-21) | Annual self-assessment & affirmation | Protect FCI, minimal risk controls |
| Level 2 (Self or C3PAO) | For handling Controlled Unclassified Information (CUI) | 110 practices with 320 objectives (aligned with NIST SP 800-171) | In limited cases: self-assessment every 3 years + annual affirmation For the majority of contractors: third-party assessment by a C3PAO every 3 years (as required in a solicitation) and annual affirmation | More substantial controls for CUI |
| Level 3 (DIBCAC / Expert) | For programs involving high-value or national security CUI | Level 2 controls + selected additional controls from NIST SP 800-172 (often ~24 extra controls) | Assessment by DIBCAC (Defense Industrial Base Cybersecurity Assessment Center) every 3 years | Designed to counter advanced persistent threats and support high priority DoD programs |
Level 1 (Self-Assessment)
CMMC Level 1 applies to organizations that handle Federal Contract Information (FCI) only. FCI is information related to contract performance that is not intended for public release but does not rise to the level of Controlled Unclassified Information (CUI).
Level 1 consists of 15 basic practices with 59 objectives aligned with FAR 52.204-21. These practices focus on fundamental cybersecurity hygiene, such as limiting system access to authorized users and protecting systems from common threats.
In practice, Level 1 environments are usually smaller and easier to scope. Annual self-assessments and affirmations are required, but there is no third-party assessment.
Where organizations run into trouble is assuming they are Level 1 without confirming whether CUI exists elsewhere in the environment, often through shared systems, email, or subcontractor workflows.
Level 2 (Self or C3PAO)
CMMC Level 2 may be required or apply to organizations that Store, Process or Transmit Controlled Unclassified Information (CUI). This level aligns directly with the 110 controls and 320 objectives of NIST SP 800-171.
A small number of Level 2 contracts may allow self-assessment, but the overwhelming majority will require a third-party assessment performed by a C3PAO. The determining factor is the solicitation language, not preference.
Level 2 environments are more complex and typically involve additional documentation, system boundary definition, and operational discipline. This is where most organizations underestimate the effort involved.
Level 3 (DIBCAC)
CMMC Level 3 applies to organizations supporting the DoD’s highest priority programs involving particularly sensitive CUI.
Level 3 builds upon Level 2 by adding selected controls from NIST SP 800-172 and requires government-led assessments conducted by DIBCAC. Organizations must already meet Level 2 requirements for the same scope.
What Level of CMMC Do I Need?
The CMMC level an organization needs depends on:
- The type of information handled
- The contracts supported
- How systems are segmented
Questions that usually clarify scope quickly:
- Do you only handle FCI? If yes, Level 1 typically applies.
- Do you handle CUI now or under future contracts? If yes, Level 2 applies.
- Is the CUI tied to high-priority or national security programs? Level 3 may be required.
- Are systems segmented? Only systems where CUI is being stored, processed or transmitted may need to meet Level 2 requirements.
Feeling Overwhelmed by the CMMC Journey? SSE Can Help.
CMMC challenges rarely come from a lack of effort. They usually come from an unclear scope.
If you are unsure which level applies to your environment, a short readiness discussion often brings clarity. The goal is to understand what actually applies and avoid unnecessary work.
SSE supports organizations throughout the CMMC process with a practical, defensible approach focused on real-world implementation.
Schedule an Initial Consultation with our team today.
Additional Blog Posts

Defense Contractors Face a New Reality as CMMC Enforcement Accelerates
With phased CMMC enforcement underway, defense contractors must act quickly to avoid compliance bottlenecks and…
The CMMC Readiness Gap: Why Many Small Manufacturers Are Unprepared
Manufacturing Tomorrow recently highlighted a growing challenge across the Defense Industrial Base — small manufacturers…
